Microsoft HTTP Protocol Stack Remote Code Execution Vulnerability - CVE-2022-21907
Hsinchu, Taiwan – Jan 18, 2022 – Last week, Microsoft published the “HTTP Protocol Stack Remote Code Execution Vulnerability - CVE-2022-21907” after it released a huge patch via Windows Update service. Of course, this huge patch has contained the fixes of CVE-2022-21907 already. All Microsoft Windows 10, Windows 11 and Windows Server 2019 users are strongly recommended to upgrade their Windows to the latest version because CVE-2022-21907 is a critical vulnerability.
By using CVE-2022-21907, cyber-criminals can send a specially crafted packet to the vulnerable Windows for remote code execution. Both web servers and clients will be impacted if the HTTP Protocol Stack “http.sys” is used for processing HTTP and HTTPS packets. For example, Microsoft Internet Information Services (IIS) uses “http.sys” by default.
| CVE Id | CVE Description | CVSS v3 Score | Severity Level | Affected MS-Windows Versions |
|---|---|---|---|---|
| CVE-2022-21907 | HTTP Protocol Stack Remote Code Execution Vulnerability. | 9.8 | Critical | Please check next table. |
Note: Microsoft Windows Server 2019 and Windows 10 version 1809 are not vulnerable by default, unless you have enabled the HTTP Trailer Support via “EnableTrailerSupport” registry value.
| Affected MS-Windows Versions | |
|---|---|
| Microsoft Windows 10 | Windows 10 Version 1809 for 32-bit Systems |
| Windows 10 Version 1809 for x64-based Systems | |
| Windows 10 Version 1809 for ARM64-based Systems | |
| Windows 10 Version 21H1 for 32-bit Systems | |
| Windows 10 Version 21H1 for x64-based System | |
| Windows 10 Version 21H1 for ARM64-based Systems | |
| Windows 10 Version 20H2 for 32-bit Systems | |
| Windows 10 Version 20H2 for x64-based Systems | |
| Windows 10 Version 20H2 for ARM64-based Systems | |
| Windows 10 Version 21H2 for 32-bit Systems | |
| Windows 10 Version 21H2 for x64-based Systems | |
| Windows 10 Version 21H2 for ARM64-based Systems | |
| Microsoft Windows 11 | Windows 11 for x64-based Systems |
| Windows 11 for ARM64-based Systems | |
| Microsoft Windows Server | Windows Server 2019 and Core Installation |
| Windows Server 2022 and Server Core Installation | |
| Windows Server 20H2 Server Core Installation |
Technical Detail of CVE-2022-21907
CVE-2022-21907 vulnerability is inside the HTTP Trailer Support feature of Windows HTTP protocol stack - “http.sys”. The “http.sys” is a kernel module of Windows. Therefore, exploiting CVE-2022-21907 and executing code remotely via “http.sys” can lead to a complete system compromise.
In most cases, assigning the DWORD registry value “EnableTrailerSupport” of “HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\HTTP\Parameters” to zero can protect your Windows against CVE-2022-21907.
CVE-2022-21907 is very similiar to the CVE-2021-31166. Both of them are HTTP protocol stack remote code execution vulnerability. The CVSS score of CVE-2021-31166 is 9.8, too. It seems the vulnerabilities of “http.sys” is not fully exploited.
Maybe some people are not familiar with HTTP trailer. HTTP trailer is defined in the Section 4.4 of RFC7230 - Hypertext Transfer Protocol (HTTP/1.1): Message Syntax and Routing. The following example is a HTTP response in HTTP chunked encoding with HTTP trailer.
HTTP/1.1 200 OK
Date: Mon, 17 Jan 2022 09:30:30 GMT
Content-Type: text/html
Transfer-Encoding: chunked
Trailer: Expires
29
<html><body><p>The file you requested is
5
3,400
23
bytes long and was last modified:
1d
Sat, 15 Jan 2022 21:12:00 GMT
13
.</p></body></html>
0
Expires: Sat, 22 Jan 2022 21:12:00 GMT
As you can see, the http header contains a key named “Trailer” and its value is “Expires”. In the trailer of HTTP body, there is a key named “Expires” and its value is “Sat, 22 Jan 2022 21:12:00 GMT”. HTTP trailer must be used in a HTTP chunked encoding message.
In the technical report, “Patch diffing CVE-2022–21907”, by Chris Hernandez, Microsoft’s CVE-2022-21907 patch contains five updated functions - UlFastSendHttpResponse, UlpAllocateFastTracker, UlpFastSendCompleteWorker, UlpFreeFastTracker and UlAllocateFastTrackerToLookaside.
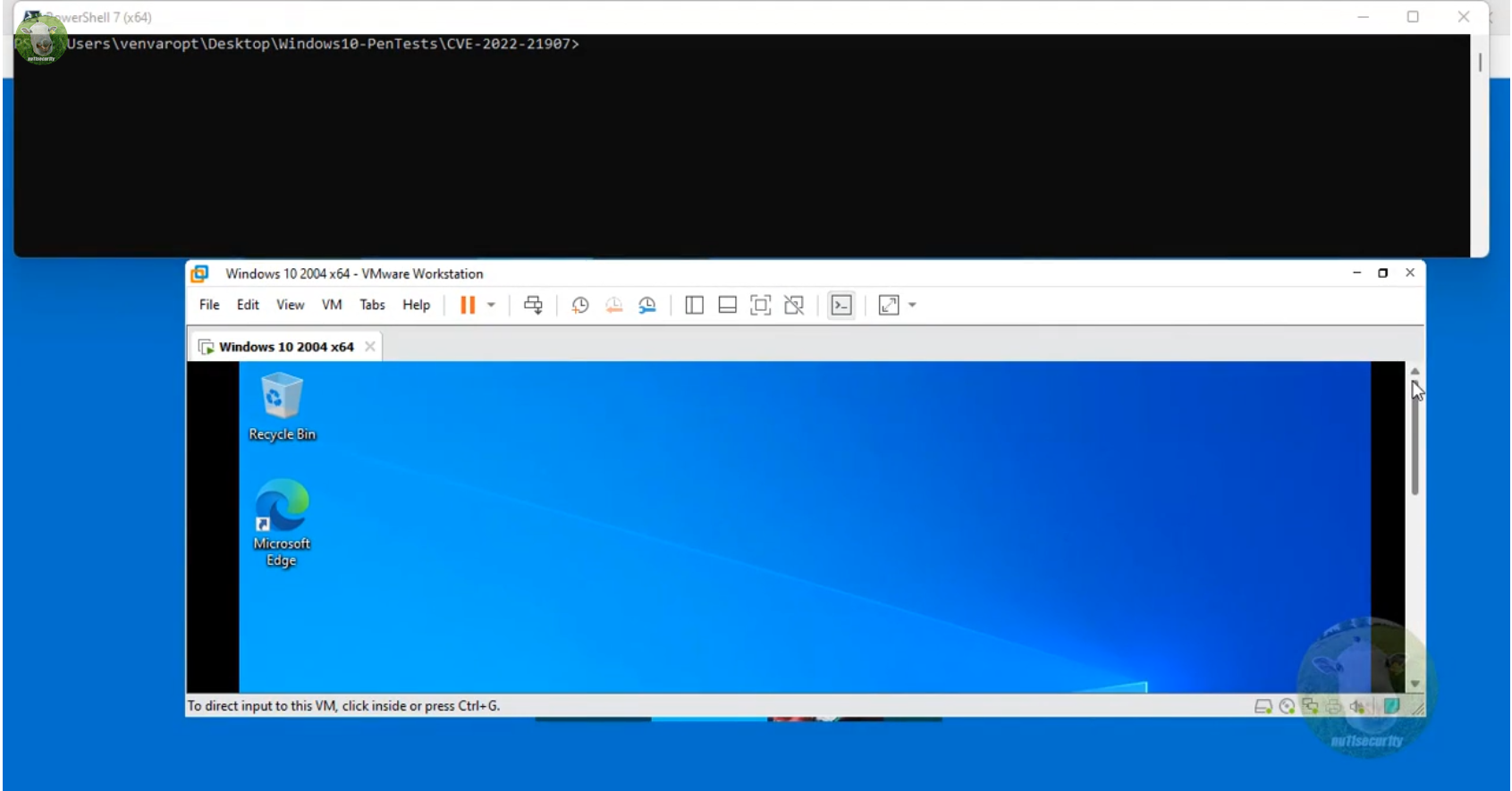
And security researcher “nu11secur1ty” has published the CVE-2022-21907 Proof of Concept. Please check that PoC for more detail.
The following is his CVE-2022-21907 PoC demo video.
Lionic’s Anti-Intrusion for CVE-2022-21907 Vulnerability
With the experience of CVE-2021-31166, Lionic understood the CVE-2022-21907 vulnerability quickly and released related signature. All Lionic security technology based products can protect against CVE-2022-21907 vulnerability after their signatures are updated to the latest version.
Partial list of Anti-Intrusion rules for CVE-2022-21907 vulnerability:
| Rule ID | Description |
|---|---|
| 8100585 | Microsoft Windows HTTP Protocol Stack Remote Code Execution |
| 8100590 | Microsoft Windows HTTP Protocol Stack Remote Code Execution |
| … | … |
Conclusion
Microsoft has prepared software patches before they published this CVE-2022-21907 security alert. Most people can upgrade their Windows easily via the Windows Update service. However, many factory machines and medical equipment are developed based on Windows. They are encapsulated as embedded system and usually operating in a closed network. Software upgrade is difficult for them.
In this situation, network administrators who manage those factory machines or medical equipment can use the Lionic Pico-UTM as the “Virtual Bug Fix”. One Pico-UTM protects one important machine. And then network administrators do not need to worry about whether their machines have any unsolved vulnerabilities or not. Besides the anti-virus and anti-intrusion rules for these brand new Windows vulnerabilities, Lionic also collected many old Windows vulnerabilities and designed related rules. Lionic Pico-UTM is cost effective and can provide full protection for your important equipment.
References:
- HTTP Protocol Stack Remote Code Execution Vulnerability, https://msrc.microsoft.com/update-guide/vulnerability/CVE-2022-21907
- CVE-2022-21907, https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-21907
- CVE-2022-21907 Proof of Concept, https://github.com/nu11secur1ty/Windows10Exploits/blob/master/2022/CVE-2022-21907/PoC/PoC-CVE-2022-21907.py
- CVE-2022-21907 demo, https://www.nu11secur1ty.com/2022/01/cve-2022-21907.html
- Patch diffing CVE-2022–21907, https://piffd0s.medium.com/patch-diffing-cve-2022-21907-b739f4108eee
- CVE-2022-21907, https://attackerkb.com/topics/xlCKfuW3a8/cve-2022-21907
About Lionic Corporation
Lionic Corporation is a worldwide provider of innovative Deep Packet Inspection solutions. The technologies of Lionic include the complete DPI-based software engine and related management software which offer the Security Solutions that addresses anti-virus, anti-intrusion, anti-webthreat; and the Content Management Solutions that addresses application identification, device identification, application based QoS, web content filtering, parental control.
Lionic’s security and content management solutions, cloud-based scan services and signature subscription service are widely deployed in the world already. They help service providers, network appliance manufacturers, semiconductor companies, etc. to enable the next generation of business routers, residential gateways, SD WAN edges and cloud gateways, advanced firewalls, UTMs, Smart NICs and mobile devices. Those products powered by Lionic provide better network management and protect the world’s networks from an ever increasing level of security threats.
Related Tags
Share This Article
Related News
News
Lionic Applauds IP Dream’s Remarkable Success: 160%+ CAGR in Cybersecurity Revenue
2025-03-18
Countermeasures Against CrazyHunter Ransomware Attack
2025-03-03
Popular AI tools are now controlled by Lionic Internet Behavior Management
2025-02-17
PHP Vulnerability CVE-2024-4577 Strikes Asia
2024-06-19
Lionic Announced AI Anti-WebThreat Technology to Combat DGA Domain-based Malware and Botnets
2024-05-23



