
Suitable for SMB and Multiple branch offices

Cybersecurity Threat Intelligence
Sustained protection against growing threats
Lionic Threat Encyclopedia compiles known intrusion attacks and offers attack data analysis and solutions
Line Notify, Auto-generated daily / weekly report
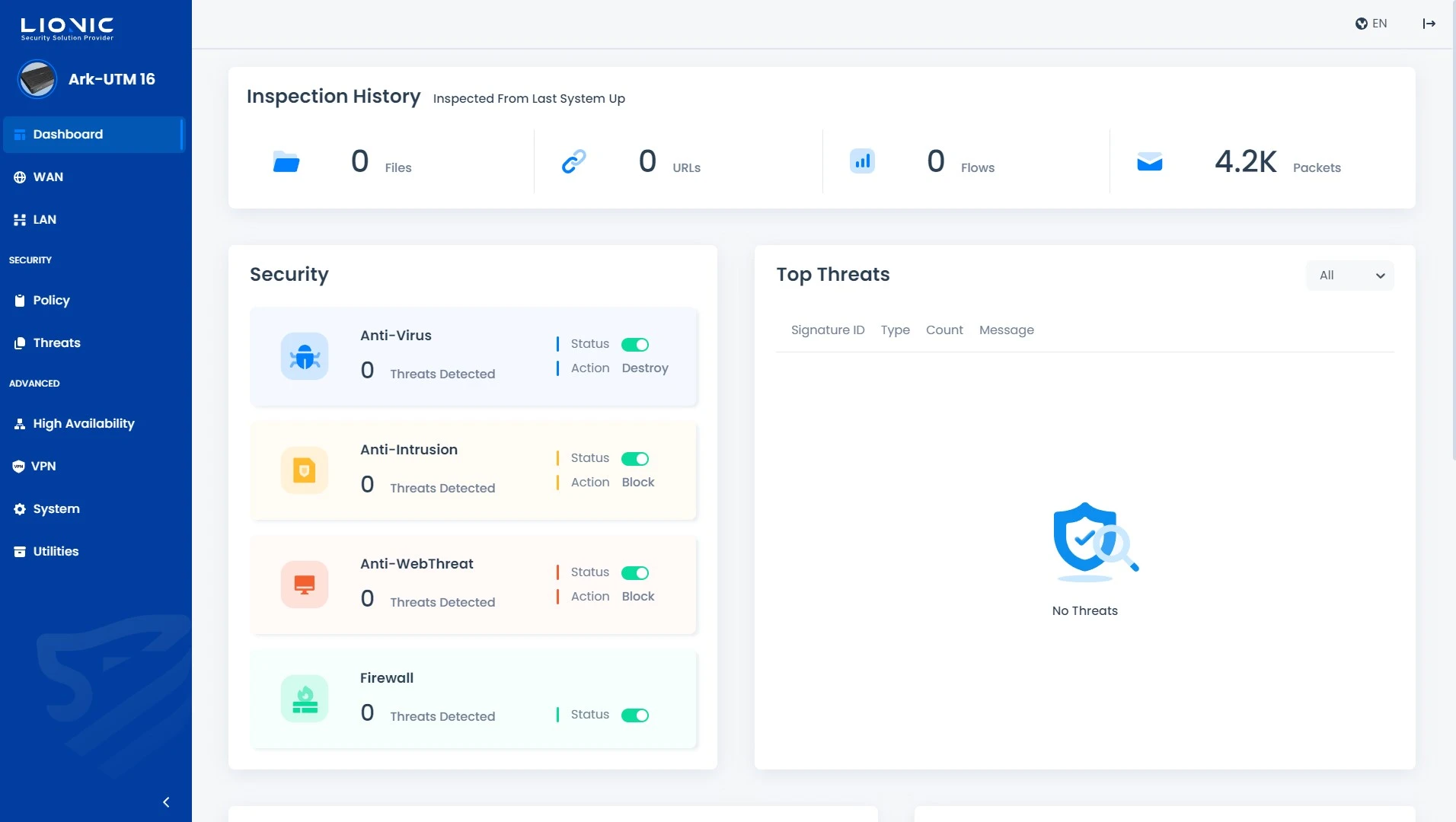
Security Monitoring + CMS
With a simple management interface and intuitive functions
Language support: Chinese, English and Japanese
Central management system (CMS) for monitoring multiple Ark-UTM 16

Segmented LAN protection
Isolates viruses within a LAN segment
Endpoint protection
Deployment in front of production equipment for protection
Remote protection
Prevent threats from infecting the internal corporate network through VPN connections